Reverse engineering & security
Specializing in binary analysis and exploit research. 5000+ hours defeating multi-layer commercial encryption and DRM systems — from bootrom to runtime.
The Research Lab

Total Ecosystem Coverage.
Our testing infrastructure spans the entire evolution of the mobile landscape. With active hardware ranging from the legacy iPhone 3GS to the latest iPhone 16 Pro, we ensure that no system, regardless of age or architecture, remains a "black box." If a vulnerability exists, we have the hardware to find it.
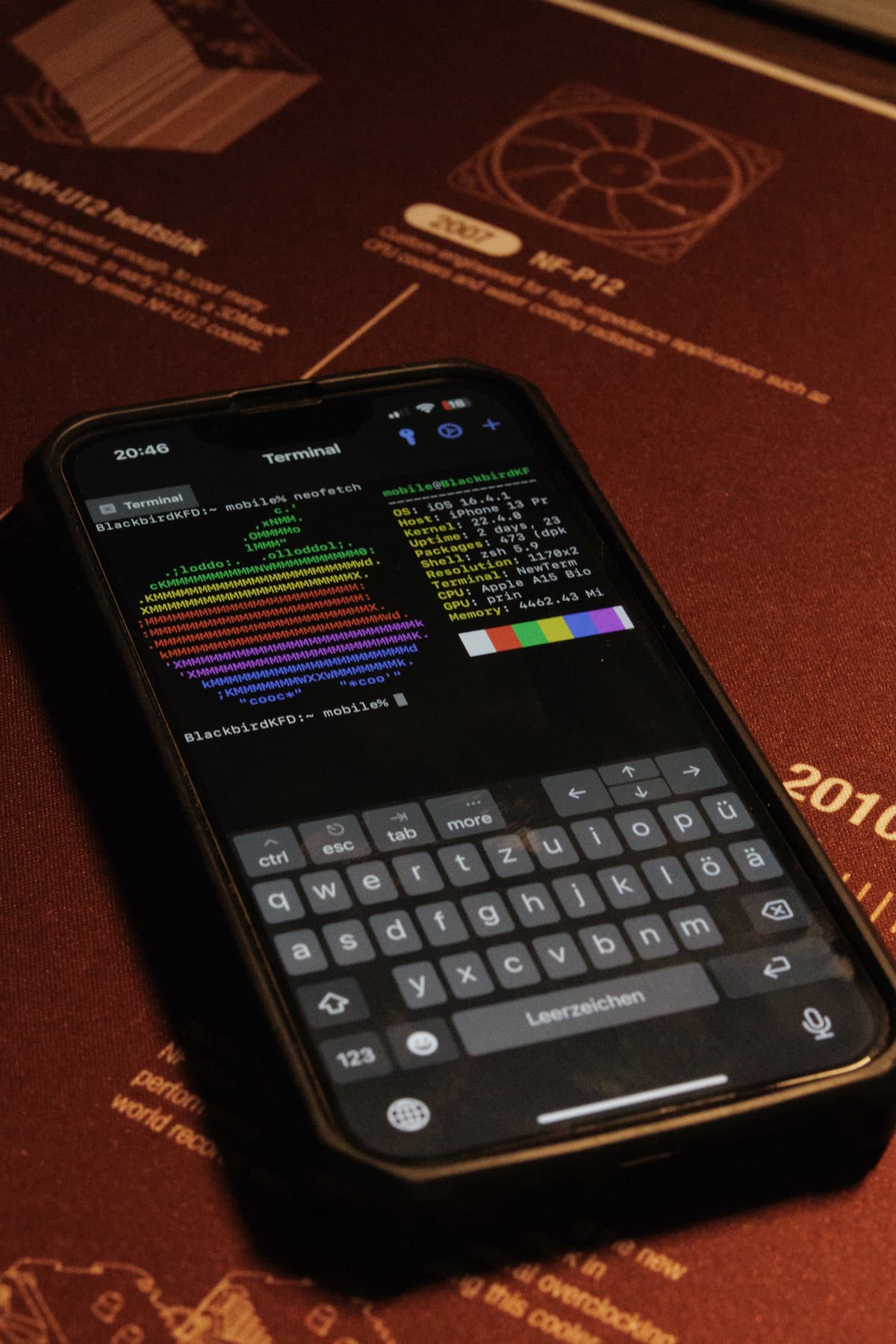
Beyond the Application Layer.
We specialize in full-stack reverse engineering, moving far beyond simple app analysis. From Bootrom-level exploits to core Firmware extraction, we deconstruct iOS at its most fundamental level to understand exactly how the silicon communicates with the software.
Native Root Authority.
For specialized research that requires bypassing standard retail restrictions, we utilize Internal Development (Dev-fused) prototypes. These units grant native, unauthorized code execution and unrestricted root access, allowing for deep-kernel debugging and hardware-level security auditing that retail units cannot provide.
Penetration testing & assessments
Full-scope security assessments, vulnerability discovery, exploit development, and secure boot bypass research. Work is conducted under clear scope and confidentiality — suitable for product security teams and authorized engagements.